Decided to watch PewDiePie’s resident evil series. Funny and fun to watch. Have to take care of the mind when doing things. Otherwise too much task and you get meh towards yourself.
I’ve been brainstorming future ideas for a generation 100 years away. Possibly 150 years. I’m not sure of what the future holds for the rest of the younger people and their children, but the way things are, it could swing either way. Its been that way ever since. Wars here and there, potential catastrophe around the corner, value this, value that. Change this change that. Its like a never ending cycle of who knows.
So I invested in a time capsule idea. My future ideas are meaningless to most people now I would think. I have no idea how they could be created. I’m not even sure whether the technology is around to make these things. I have also noticed that time is cruel in this world. People seem to dedicate their entire life to one direction, and it seems to either create a lineage for someone else to follow or they become a mention in wikipedia.
I bought some unique plant seeds that have the potential to help future generations due to the varied medicinal and water purification abilities. That would probably be another investment towards another’s future. If the world becomes a horrible place and inhospitable in certain places, I managed to find what it takes to correctly terraform an area. Meaning proper atmospheric conditions for living. Managed to also fund an idea into life seeds.
You have no idea what that is because, well, I’m only just telling you. A life seed can be planted in an area that has no life really, just conditions suitable after terraforming had occurred. The seed would rapidly generate life sources and other forms within water and the surrounding area. Algae would also be part of this rapid growth process. The reason is that those produce more oxygen and help life survive in water ways. Can you image this?
My forest seed would rapidly deploy native species to that area including soil molecules, microbes and worm eggs to help increase the soil quality. So the 2 types of seeds would rapidly deploy life sources to land and water to help rehabilitate that area and make it alive again. This of course would be generation one of the seed pods – so they in turn through enhanced genetics would spawn rapidly for 2 to 3 generations, and then return to their prior growth rates. Hence, advanced genetics.
I managed to also come up with an idea that guns vs robots wont be the only way should we happen to become victims of them. Swords are very useful. This isn’t a photon sword or chemically laced sword, it is simply robust enough to cut fluid lines and armour. Very simple thought.
I have to think about the future, even of this blog. Noone is reading it right now, so that’s fine. It has honestly been the story of my life. Have great ideas, be ignored. It isn’t a sad song, just an honest statement.
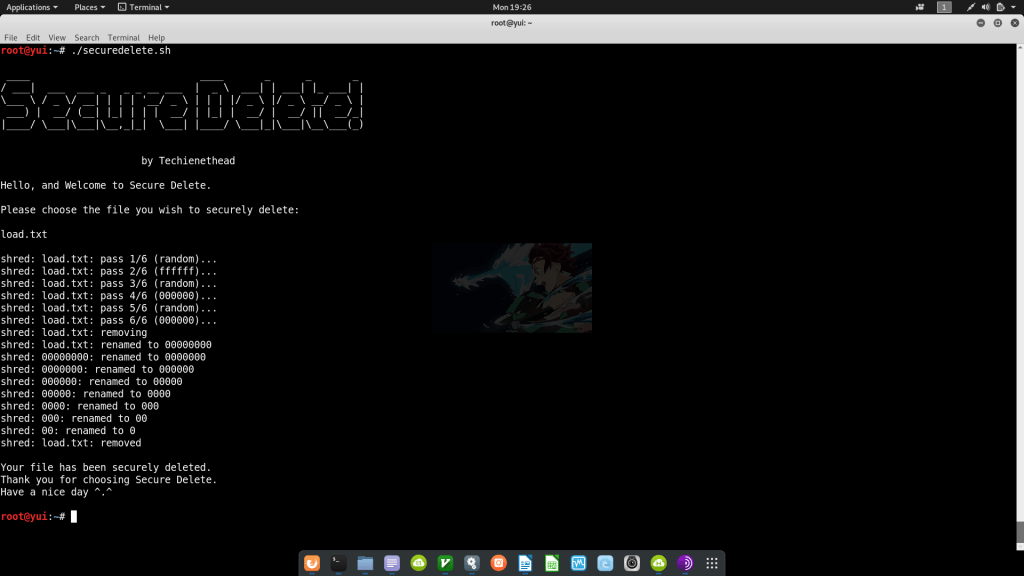
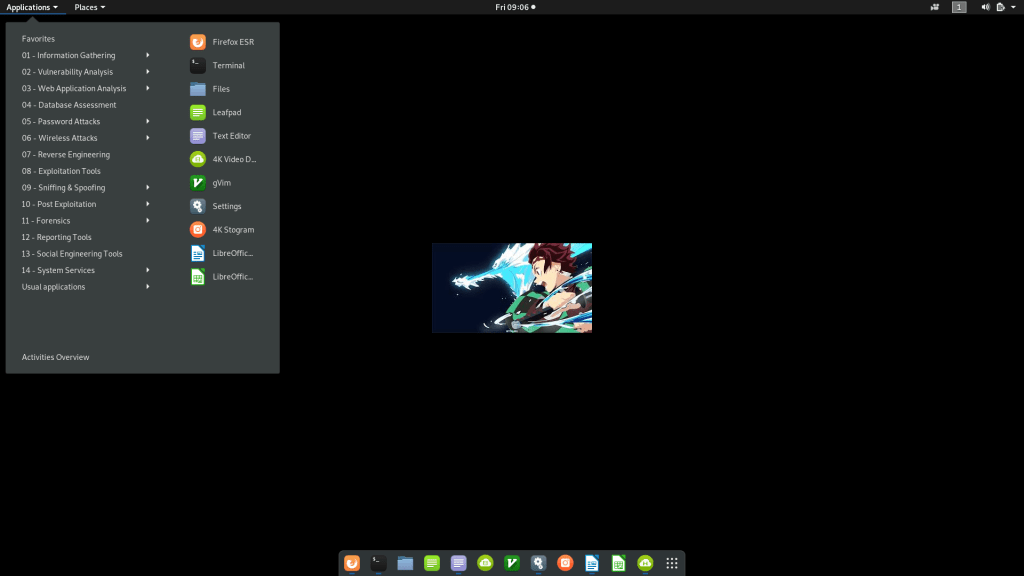
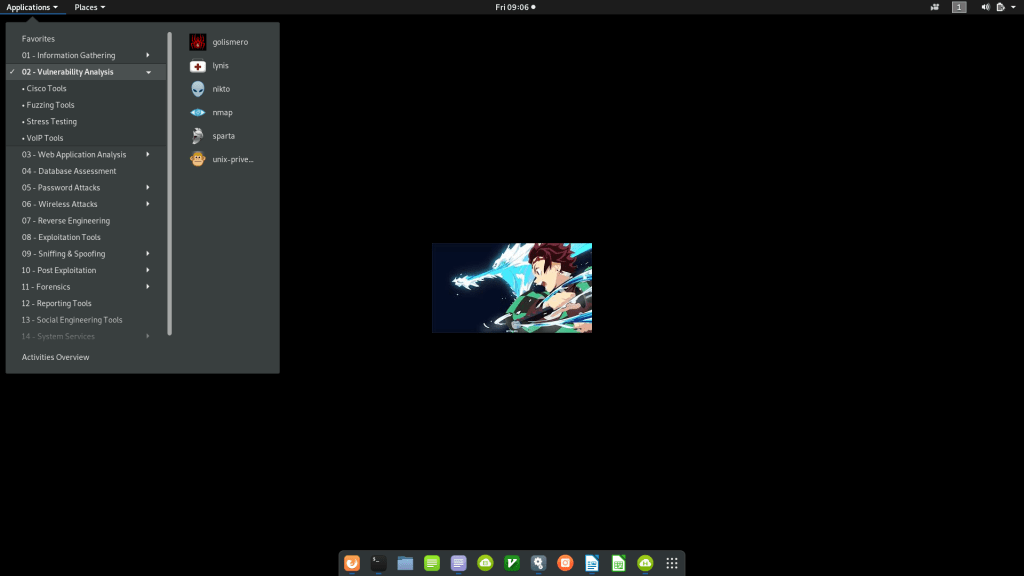
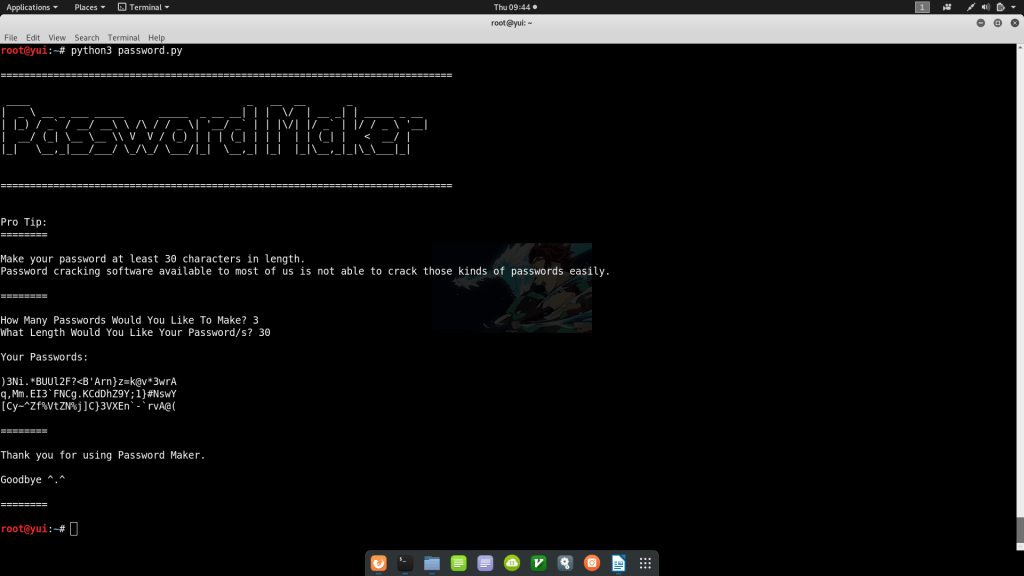
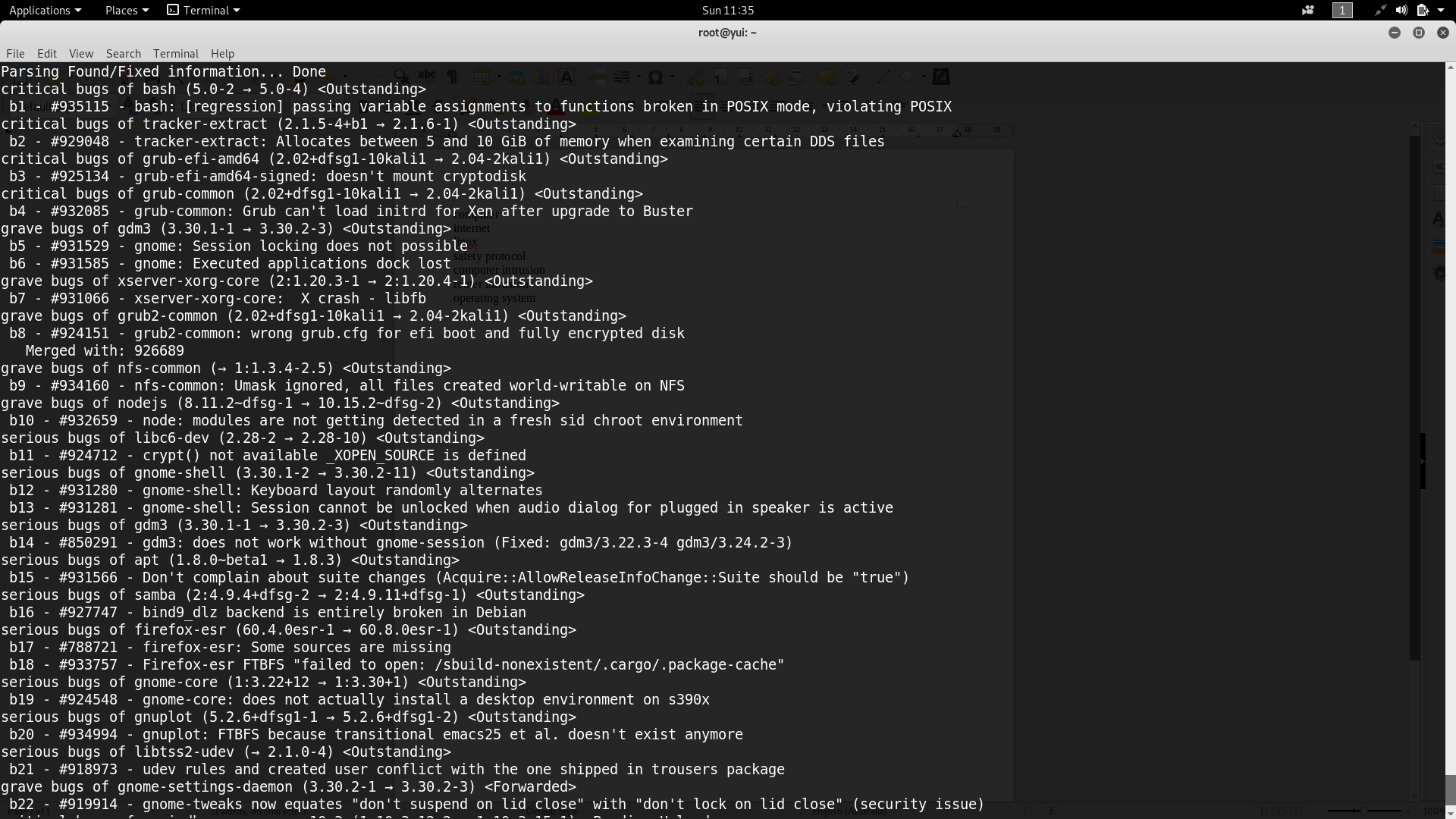
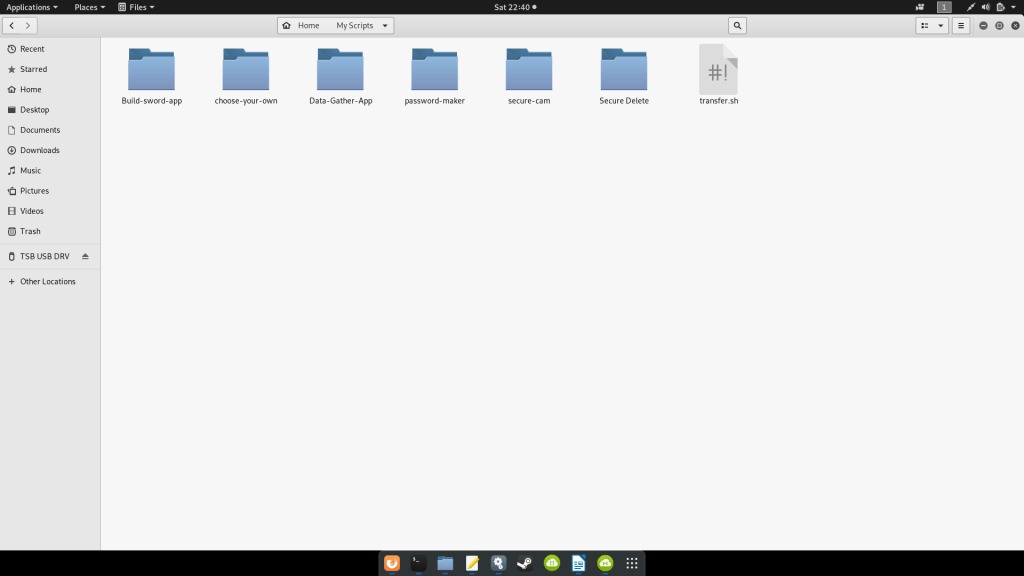
On the flip side I coded as well. Am even going to teach myself Java. The apps looked nicer in Java than in Python. Even though Python seems to be great with machine learning, which is what everyone else is doing. So with all that said and done, my code ‘junk pile’ looks like the image above. Nothing too serious, but some great potential. Oh and I managed to get my camera working in Python. Once again, I don’t think the wearable is there yet. I could create it, but it’s probably better to deploy a sustainable drone that can accompany a person places.
Something organic. That’s right, an organic drone that can survive on sunlight, dark light and even just normal light. There’s another wonderful idea. Not biological, organic. Think about it.